Makaleler
52
Tümü (52)
SCI-E, SSCI, AHCI (26)
SCI-E, SSCI, AHCI, ESCI (36)
ESCI (10)
Scopus (27)
TRDizin (26)
Diğer Yayınlar (4)
10. The Battle of Chatbot Giants: An Experimental Comparison of ChatGPT and Bard
Uluslararası Mühendislik Araştırma ve Geliştirme Dergisi
, cilt.16, sa.2, ss.679-691, 2024 (TRDizin)


19. Detection and classification of darknet traffic using machine learning methods Karanlik aǧ trafiǧinin makine öǧrenmesi yöntemleri kullanilarak tespiti ve siniflandirilmasi
Journal of the Faculty of Engineering and Architecture of Gazi University
, cilt.38, sa.3, ss.1737-1746, 2023 (SCI-Expanded, Scopus, TRDizin)










20. Malware detection using image-based features and machine learning methods Görüntü tabanli özelliklerden ve makine öǧrenmesi yöntemlerinden faydalanilarak kötücül yazilim tespiti
Journal of the Faculty of Engineering and Architecture of Gazi University
, cilt.38, sa.3, ss.1781-1792, 2023 (SCI-Expanded, Scopus, TRDizin)








22. IoT based mobile driver drowsiness detection using deep learning
JOURNAL OF THE FACULTY OF ENGINEERING AND ARCHITECTURE OF GAZI UNIVERSITY
, cilt.37, sa.4, ss.1869-1881, 2022 (SCI-Expanded, Scopus, TRDizin)








25. A new classification method for encrypted internet traffic using machine learning
TURKISH JOURNAL OF ELECTRICAL ENGINEERING AND COMPUTER SCIENCES
, cilt.29, sa.5, ss.2450-2468, 2021 (SCI-Expanded, Scopus, TRDizin)








27. AppPerm Analyzer: Malware Detection System Based on Android Permissions and Permission Groups
INTERNATIONAL JOURNAL OF SOFTWARE ENGINEERING AND KNOWLEDGE ENGINEERING
, cilt.30, sa.3, ss.427-450, 2020 (SCI-Expanded, Scopus)




28. TWİTTERDA VERİ MADENCİLİĞİ YÖNTEMLERİN KULLANARAK BOT TESPİTİ
International Journal on Mathematic, Engineering and Natural Science
, cilt.3, sa.11, ss.98-108, 2019 (Hakemli Dergi)
31. Permission-based Android Malware Detection System Using Feature Selection with Genetic Algorithm
INTERNATIONAL JOURNAL OF SOFTWARE ENGINEERING AND KNOWLEDGE ENGINEERING
, cilt.29, sa.2, ss.245-262, 2019 (SCI-Expanded, Scopus)




32. Permission-Based Malware Detection System for Android Using Machine Learning Techniques
INTERNATIONAL JOURNAL OF SOFTWARE ENGINEERING AND KNOWLEDGE ENGINEERING
, cilt.29, sa.1, ss.43-61, 2019 (SCI-Expanded, Scopus)




35. Makine Öğrenmesi Algoritmalarıyla Android Kötücül Yazılım Uygulamalarının Tespiti
Süleyman Demirel Üniversitesi Fen Bilimleri Enstitüsü Dergisi
, cilt.22, sa.2, ss.1087-1094, 2018 (TRDizin)
37. Development of Reserved Reliable Flow Control Algorithm in Mobile Ad Hoc Networks
Gazi Journal of Engineering Sciences
, cilt.4, sa.3, ss.144-156, 2018 (TRDizin)
38. Kablosuz Ağlarda Çok Katmanlı Güvenlik ve Performansa Etkisi
Karaelmas Fen ve Mühendislik Dergisi
, cilt.8, sa.1, ss.126-137, 2018 (TRDizin)
40. Androıd Kötücül Yazılım Tespiti Yaklaşımları
Uluslararası Bilgi Güvenliği Mühendisliği Dergisi
, cilt.3, sa.2, ss.48-58, 2017 (Hakemli Dergi)
41. Büyük Ölçekli Veri Merkezleri İçin Bulut Bilişim Kullanarak Sunucu Sanallaştırma
Gazi Mühendislik Bilimleri Dergisi
, cilt.3, sa.1, ss.20-26, 2017 (TRDizin)
43. Permission based detection system for android malware
JOURNAL OF THE FACULTY OF ENGINEERING AND ARCHITECTURE OF GAZI UNIVERSITY
, cilt.32, sa.4, ss.1015-1024, 2017 (SCI-Expanded, Scopus, TRDizin)






44. Android Kötücül Yazılım Tespit Sistemleri İncelemesi
Duzce University Journal of Science Technology
, cilt.5, sa.2017, ss.281-298, 2017 (TRDizin)
45. Analyzing the Route Cache Timeout Parameter of DSR Protocol in Mobile Ad Hoc Networks
International Journal of Computer and Communication Engineering (IJCCE)
, cilt.6, sa.1, ss.40-48, 2017 (Hakemli Dergi)


46. Android Mobil Uygulamalar için İzin Karşılaştırma Tabanlı Kötücül Yazılım Tespiti
Politeknik Dergisi
, cilt.20, sa.1, ss.175-189, 2017 (TRDizin)
47. Mobil Kötücül Yazılımlar ve Güvenlik Çözümleri Üzerine Bir İnceleme
Gazi Üniversitesi Fen Bilimleri Dergisi Part: C Tasarım ve Teknoloji
, cilt.4, sa.2, ss.49-64, 2016 (TRDizin)
49. Android Kötücül Yazılım Tespit ve Koruma Sistemleri
Erciyes Üniversitesi Fen Bilimleri Enstitüsü Dergisi
, cilt.31, sa.1, ss.9-16, 2015 (TRDizin)
50. DEVELOPMENT OF 3G BASED REMOTE CONTROLLED CAR
JOURNAL OF THE FACULTY OF ENGINEERING AND ARCHITECTURE OF GAZI UNIVERSITY
, cilt.27, sa.1, ss.135-142, 2012 (SCI-Expanded, Scopus)




51. Hareketli Ad-Hoc Ağlarda Bir Hareketlilik YönetimiProtokolü
Politeknik Dergisi
, cilt.11, sa.4, ss.313-38, 2008 (TRDizin)
Hakemli Bilimsel Toplantılarda Yayımlanmış Bildiriler
37
7. Docker Konteyner Teknolojisi Üzerine YapılanGüvenlik Çalışmalarının İncelemesi
12. Uluslararası Bilgi Güvenliği ve Kriptoloji Konferansı, Ankara, Türkiye, 16 - 17 Ekim 2019, (Tam Metin Bildiri)
9. Categorization of Claims and Complaints from Mavimasa (Bluetable) Social Network Address by Using Machine Learning
3rd International Mediterranean Congress on Natural Sciences, Health Sciences and Engineering (MENSEC III), 18 - 20 Haziran 2019, (Tam Metin Bildiri)
10. A Smart Lighting Control System Using Solar Energy in The Scope of Internet of Things
3rd International Symposium on Innovative Approaches in Scientific Studies, Ankara, Türkiye, 19 - 21 Nisan 2019, (Tam Metin Bildiri)
11. Twıtter’da tweet ve hesap tabanlı spam tespiti
ICAIME 2019- Yapay Zeka ve Uygulamalı Matematik 2019 Uluslararası Konferansı’xx, Antalya, Türkiye, 20 - 22 Nisan 2019, cilt.1, ss.898-905, (Tam Metin Bildiri)
27. Mobil Uygulamaların Sınıflandırılmasında Kullanılan Makine Öğrenmesi Algoritmalarının Güvenirlilik Tespiti
9. ULUSLARARASI BİLGİ GÜVENLİĞİ VE KRİPTOLOJİ KONFERANS, Ankara, Türkiye, 25 - 26 Ekim 2016, ss.191-194, (Tam Metin Bildiri)
29. Mobil Platformlarda Gizli Ağ Saldırılarının Önlenmesi Ve Mobil Uygulaması
VIII. Uluslararası Bilgi Güvenliği ve Kriptoloji Konferansı (ISCTurkey2015), Ankara, Türkiye, 30 - 31 Ekim 2015, (Tam Metin Bildiri)
30. Mobil Cihazlarda Zararlı Yazılım TespitindeKullanılan Statik Analiz Araçları
8. ULUSLARARASI BİLGİ GÜVENLİĞİ VE KRİPTOLOJİ KONFERANS, Ankara, Türkiye, 30 - 31 Ekim 2015, (Tam Metin Bildiri)
33. Remote Access Cisco CCNA Laboratory
5th World Conference on Educational Sciences(WCES-2013), ROMA, İtalya, 6 - 08 Şubat 2013, (Tam Metin Bildiri)
37. Genetic Algorithm Based Location Optimization of Emergency Service Units
4th FAE International Symposium, European University of Lefke, 1 - 03 Ocak 2006, (Tam Metin Bildiri)
Kitaplar
3
1. Tweet and Account Based Spam Detection on Twitter
Lecture Notes on Data Engineering and Communications Technologies: Artificial Intelligence andApplied Mathematics in Engineering Problems, D. Jude Hemanth,Utku Kose, Editör, Springer, İSPANYA, ss.898-905, 2020
2. Analysis of MODBUS Protocol Vulnerabilities with ModbusPalSimulator
CURRENT ACADEMIC STUDIES IN ENGINEERING SCIENCES-2018, Prof. Dr. Serdar SALMAN, Doç. Dr. Duygu KAVAKDr. Ali KILIÇER, Editör, IVPE, Cetinje, ss.184-202, 2018
3. Mobil Cihazlarda Siber Güvenlik
Siber Güvenlik ve Savunma Farkındalık ve Caydırıcılık, Şeref Sağıroğlu, Mustafa Alkan, Editör, Grafiker, Ankara, ss.311-346, 2018
Metrikler
Yayın (WoS)
50
Yayın (Scopus)
47
Atıf (WoS)
477
H-İndeks (WoS)
11
Atıf (Scopus)
771
H-İndeks (Scopus)
14
Atıf (Scholar)
1374
H-İndeks (Scholar)
17
Atıf (TrDizin)
12
H-İndeks (TrDizin)
2
Atıf (Sobiad)
14
H-İndeks (Sobiad)
1
Atıf (Diğer Toplam)
16
Proje
6
Tez Danışmanlığı
19

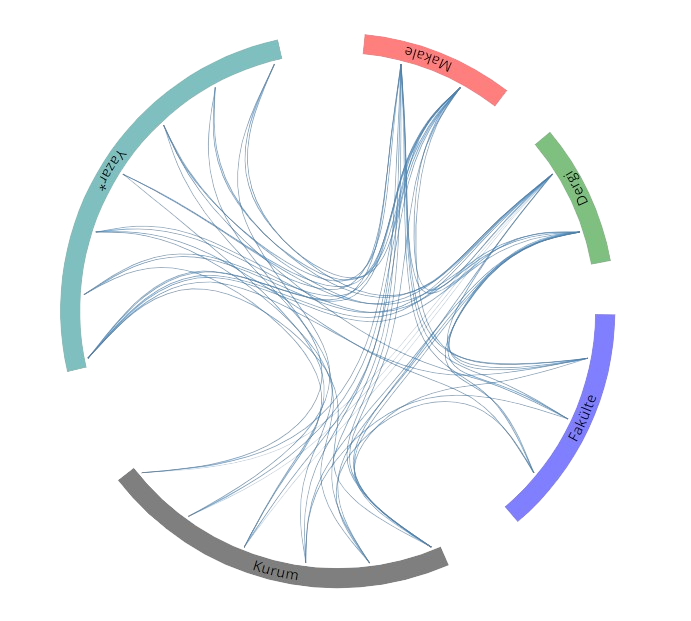 Yayın Ağı
Yayın Ağı









